On Tuesday, June 27th, the third wave of major ransomware attacks struck Europe and then the United States. Ransomware is a type of malicious software, also known as malware, which is designed to block access to a computer system until a sum of money is paid. Early analysis of the malware code assumed that it was a old piece of ransomware called Petay, but after further analysis it was determine that the code was much different. The new ransomware has been named NotPetay. The real question with this most recent ransomware attack is not the name, but what type of attack it really was.
NotPetay takes over computer systems by encrypting the hard drive on the system. The threat agent then requests a payment of $300 worth of Bitcoin in return for a digital key to unlock the user’s encrypted data. No reports have been published stating that a victim has received a key in exchange for payment of the ransom. As of today, according to Forbes, “the hacker’s email account used to handle payment and provide encryption keys has been closed.”
As with all malware outbreaks, we suggest a few steps that users can take to lessen the chance of being infected. First, make sure your operating system is up to date with all the latest patches and firmware updates. Additionally, update your antivirus signature database. Furthermore, make sure your data is backed up. Backing up your data is key, because with a backup the system can just be wiped back to the factory image. Here at Thornton Technology we suggest taking a redundant backup approach using both cloud and physical storage to do your routine backups.
NotPetay is an important attack. It is important not because it was large or caused the most damage. The importance of this latest ransomware attack is that it might not have been ransomware attack at all, well at least not in the conventional way that most of us think about ransomware attacks. It is believed that the attack was carried out by a state sponsored actor under direction of the Russian government. With the first wave of the attack focusing mainly on Ukrainian power grids, government buildings, and financial institutions, it is not a stretch of the imagination. Over 60 percent of those affected have been located inside Ukraine with most targets having ties to the country’s government. Ransomware has traditionally targeted random users for financial gain… not with the intent of causing harm through an act of cyber warfare.
On July 4th, a message was posted on DeepPaste, a Tor-only announcement board. The post requested 100 bitcoin or $250,000 USD for the private encryption key to NotPetay.
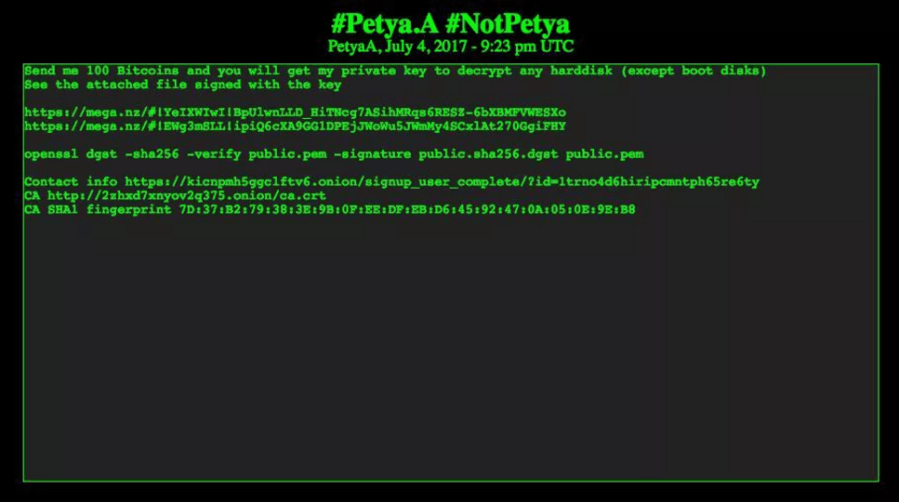
In addition, the message included a file signed with NotPetay’s private key, which would indicate that the message did originate from the creator of NotPetay or at the very least someone that was able to obtain the private key. The real question is, why would they wait until over a week after the initial infections and at a time when most of those impacted have recovered. Moreover, at this point most antivirus and operating system companies have released signature and/or patches to combat the impact of NotPetay.
